Enterprise-Grade TPRM with Cognitive Compliance and Risk Intelligence
ShieldRisk.ai empowers organizations with robust capabilities that simplify, automate, and strengthen the entire third-party risk management (TPRM) lifecycle.
Schedule ShieldRisk Demo
Building Trust Through Intelligent Risk Management
Modern enterprises depend on thousands of vendors - each a potential entry point for data compromise or regulatory exposure. ShieldRisk.ai uses artificial intelligence and predictive analytics to automate Third-Party Risk Management (TPRM), bridging the gap between vendor compliance and business resilience.
Aggregates vendor data to predict emerging risks.

Highlights missing clauses & compliance gaps using NLP.

Calculates contextual cyber, financial & privacy risk.

Auto-maps controls to ISO, SOC, GDPR, DPDPA & more.

Correlates vendor software with known vulnerabilities.

Tracks vendor breaches & financial health in real time.
Al-Driven TPRM Ecosystem
Each layer of ShieldRisk.ai strengthens enterprise trust - turning risk visibility into measurable assurance.
Capability
ShieldRisk.ai
Traditional Tools
Al-Driven Risk Scoring
Contract Intelligence
Continuous Monitoring
Automated Compliance Mapping
Integrated Dashboard
Vendor Collaboration Portal
Third + Fourth-Party Risk
Predictive Analytics
Governance Automation
Evidence Repository
Protect Your Enterprise.
Leverage Al-driven visibility to strengthen vendor relationships, meet compliance expectations, and safeguard your digital supply chain.


Delivering impactful cybersecurity awareness programs, trusted by organizations to strengthen their human firewall.

Challenges & Standardized Framework
Disjointed Data Sets
Vendor information is scattered across multiple spreadsheets without a standardized assessment framework.
Diverse Vendor Privacy Practices
Vendors handling different types of personal and confidential data (PII, PHI, financial) require tailored assessments.
Manual Risk Analysis Processes
Evaluating security frameworks and control effectiveness manually leads to delays and oversight.
Resource-Heavy Assessment Cycles
Procurement, Quality, and Audit teams face repetitive, time-consuming efforts to assess each vendor.
Vendor Governance & Risk Lifecycle
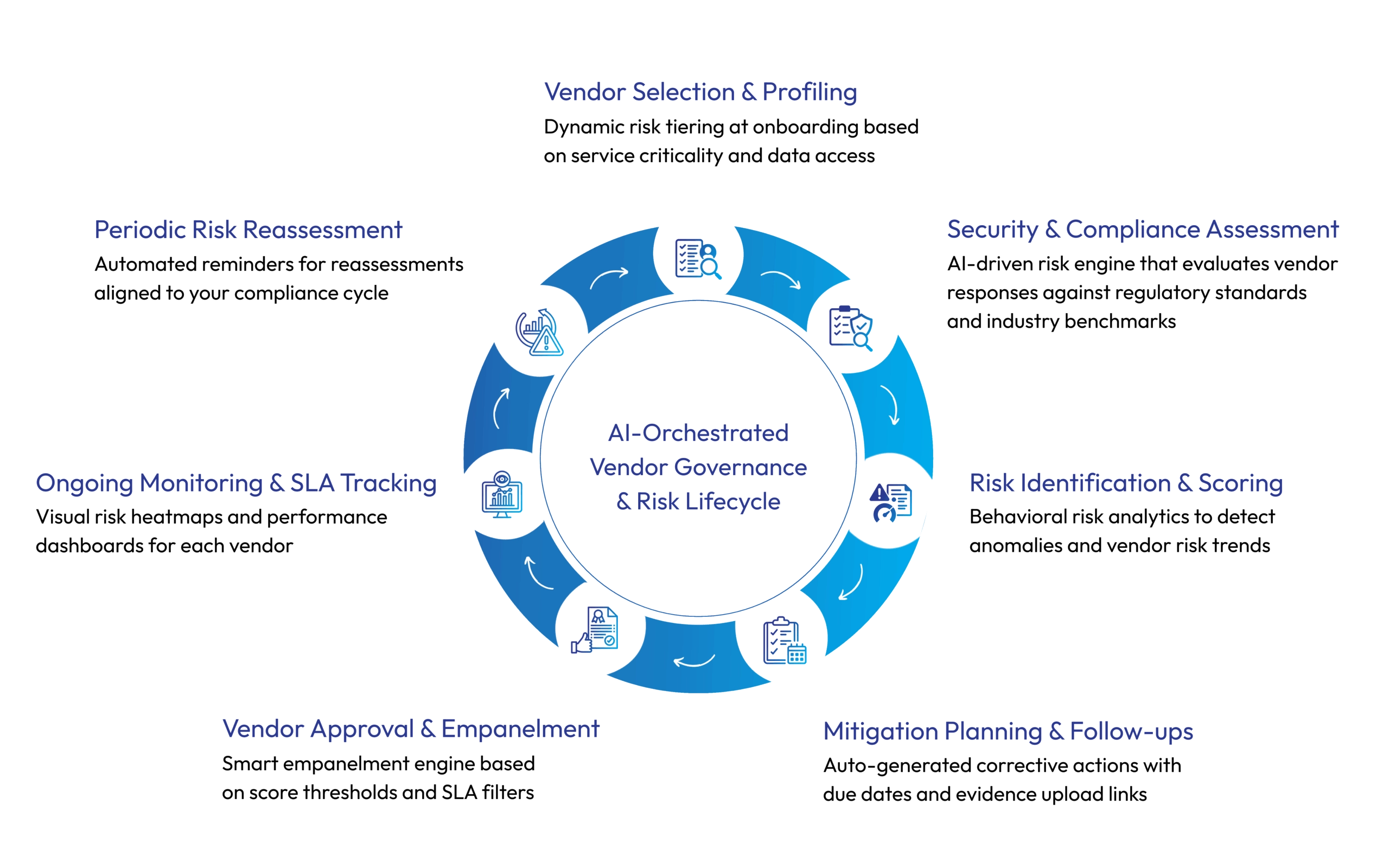
Key Features
Cognitive Risk Scoring Engine
ShieldRisk.ai’s intelligent engine evaluates the overall risk associated with third-party vendors using real-time data, predictive analytics, and AI-driven algorithms. Rather than relying solely on static assessments, our platform continuously updates vendor risk profiles based on changes in threat intelligence, regulatory landscape, and vendor behavior.

Pre-Built Compliance Packs
We simplify compliance for organizations operating under multiple regulatory regimes by offering pre-configured templates and assessment packs. These are aligned with global standards and include the necessary control checks, questionnaire sets, and evidence collection modules.

Interactive Dashboards & Risk Heatmaps
Visualize your vendor ecosystem using interactive dashboards that provide deep insight into third-party risks, performance metrics, and compliance status. These tools help risk managers, CISOs, and board-level executives instantly make data-driven decisions.

Centralized Evidence Repository
Managing and retrieving vendor documents during audits can be time-consuming. ShieldRisk.ai offers a secure, centralized repository to collect, store, and manage all necessary evidence, making your audit preparation seamless.

Audit-Ready Reports & Certifications
Generate professional, downloadable reports for regulators, internal audits, and executive boards. All decisions—approvals, exceptions, accepted risks—are captured and reported with justifications, timelines, and supporting evidence. These reports make your organization always audit-ready and transparent.

Vendor Tiering & Lifecycle Management
ShieldRisk.ai facilitates risk-aligned vendor segmentation by assessing factors such as organizational impact, data sensitivity, and access privileges—enabling strategic oversight and lifecycle management tailored to each vendor's risk profile. This structured lifecycle approach ensures reduced exposure, faster onboarding, and compliant exits.
Elevate your organization’s security posture with cybersecurity training and phishing to build a human firewall.
Copyright © 2025 ShieldByte Infosec Pvt. Ltd.| All Rights Reserved