SOC 2 Compliance and Attestation Services
The SOC 2 (System and Organization Controls 2) framework, developed by the American Institute of Certified Public Accountants (AICPA), evaluates an organization’s information security posture based on Trust Service Criteria (TSC) — Security, Availability, Processing Integrity, Confidentiality, and Privacy. It is a key requirement for technology service providers, SaaS platforms, data centers, and cloud-based organizations handling customer data.
At Shieldbyte Infosec, we help organizations achieve SOC 2 Type I and Type II compliance, ensuring that their information systems meet the highest standards of security and governance. Our structured audit and readiness program aligns with requirements to help organizations strengthen their internal controls, mitigate risks, and build stakeholder trust.
Our team of SOC assurance specialists and cybersecurity auditors provides complete lifecycle support — from gap assessment and control mapping to evidence testing and auditor coordination. We help organizations design control frameworks that are practical, scalable, and aligned with global compliance expectations.
a) SOC 2 Type I reports evaluate the design and implementation of controls at a specific point in time.
b) SOC 2 Type II reports assess both design and operational effectiveness over a defined audit period (typically 6–12 months).
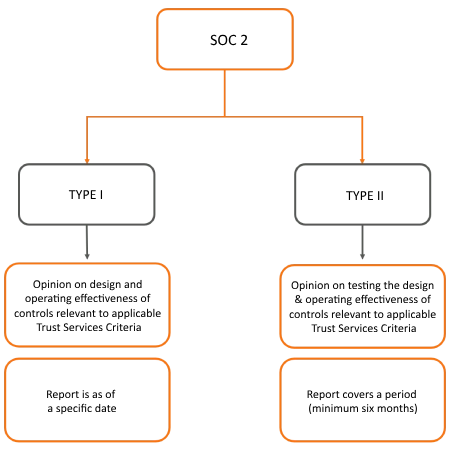
We guide clients through a structured roadmap that ensures control maturity, audit readiness, and stakeholder confidence for both Type I and Type II compliance
Our Approach

Gap Assessment and Readiness Review
Analyzing current security, availability, and privacy controls against SOC 2 requirements to identify compliance gaps and define remediation priorities.

Control Framework Mapping
Mapping existing controls to the five Trust Service Criteria and aligning them with organizational objectives and regulatory obligations.

Policy and Documentation Review
Evaluating information security policies, procedures, and control documentation to ensure alignment with SOC 2 standards and auditor expectations.

Control Design and Implementation (Type I)
Assessing the design and implementation of controls at a specific point in time to achieve SOC 2 Type I compliance.

Operational Effectiveness Testing (Type II)
Conducting evidence-based control testing over a 6–12-month period to validate operational performance and reliability.

Evidence Collection and Validation
Compiling and validating logs, reports, and system evidence to demonstrate control functionality and audit readiness.

Remediation and Improvement Planning
Providing actionable recommendations to address control weaknesses, enhance monitoring, and strengthen documentation.

External Audit Coordination
Facilitating coordination with independent auditors, supporting fieldwork, and ensuring smooth completion of the examination process.

Continuous Monitoring and Governance
Establishing ongoing compliance tracking and control monitoring programs to maintain readiness for future SOC 2 assessments.
Why Choose Shieldbyte Infosec?
CERT-In Empanelled
Recognized by the Government of India for security audits.
Proven Expertise
350+ clients across banking, IT, insurance, healthcare, and manufacturing.
End-to-End Support
From scoping to remediation and final certification.
Let’s Strengthen Your Cyber Defenses
Enhance protection, reduce risk, and support your growth objectives